Consistent, Scalable, and Flexible Automation Solutions for Device Onboarding
Fragmented processes, disparate systems, and manual configurations leave organizations vulnerable to security gaps and inconsistent performance. Poorly configured or insecure devices can lead to data breaches, and other security risks highlighting the critical need for a more integrated approach. With teams spread across locations and relying on varied tools, traditional manual methods are no longer sufficient to handle today’s demands. Modern IT operations requires streamlined, device onboarding automated to ensure consistency, security, and scalability across the entire network.
Key Challenges to Device Onboarding
Manual Processes and Human Error
Device onboarding involves numerous manual configurations, such as assigning IP addresses, configuring security settings, and ensuring compliance with policies. Each manual step introduces the risk of human error and significant time, especially when scaling across hundreds or thousands of devices. This can lead to delays in operations, particularly when onboarding new users or deploying new equipment during IT expansions or upgrades.
Complex Network Configurations
Complex network configurations complicates device onboarding, as each device must be tailored to meet unique network settings like VLANs, subnets, and security protocols. This often leads to inconsistent configurations, extended setup times, and a higher risk of errors. Manual processes struggle to keep up with this complexity, making automation essential to ensure accuracy, speed, and consistency across all devices.
Lack of Standarization
Without standardized processes, teams adopt different methods for onboarding devices, leading to configuration discrepancies. This can complicate troubleshooting and raise the risk of non-compliance with company standards and security protocols. Improperly configured devices that do not meet security requirements can create vulnerabilities in the network’s defense. Manual verification of compliance for every device can be challenging, especially in environments with diverse device types.
Scalability Challenges
As organizations grow and networks expand, the process of onboarding devices manually can become a bottleneck. Scaling these processes without the right tools in place can be highly resource-intensive and prone to delays. Manually tracking the onboarding status and configurations of multiple devices across the network can be difficult. This lack of visibility can result in inefficient troubleshooting and poor network management.
Transforming Device Onboarding with Automation
Solving Configuration Management Database compliance requires a structured approach that combines governance, automation, regular audits, and continuous improvement. By integrating compliance checks into the CMDB lifecycle and leveraging discovery tools to automate data accuracy, organizations can maintain a compliant and reliable CMDB that aligns with internal and regulatory standards.
ADepT: A Platform Built for Seamless Compliance
End to End Automation
Automating processes across your entire IT stack reduces human error and ensures consistency in CMDB data. Comprehensive automation simplifies the management of your IT infrastructure, enabling seamless updates and accurate insights.
ADepT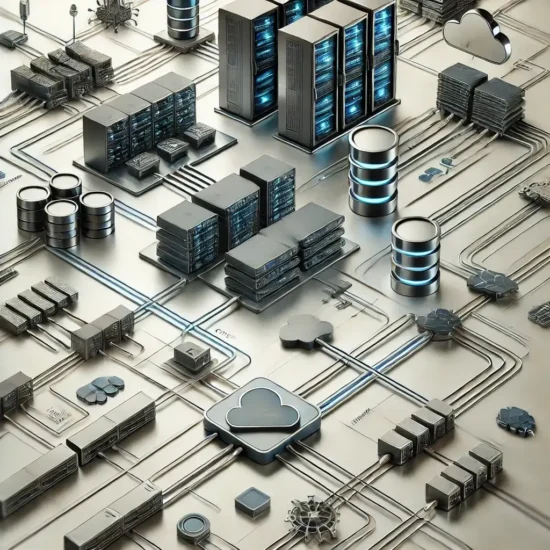

AI Driven Discovery
Leverage AI-driven discovery to automatically uncover and track assets within your infrastructure. This capability provides real-time insights into existing configurations, enhancing your ability to manage and maintain compliance effectively.
ASCOT

Flexible Language Agnostic Platform
of companies use three or more automation platforms. Our language-agnostic platform seamlessly integrates automation across any environment, adapting to your unique needs without language or tool limitations.
